With online activity becoming a staple in our daily routines, keeping our personal information safe is more important than ever. From shopping to banking, we can easily expose sensitive information to prying eyes – and with the rise of online crimes, malicious attacks can happen to anyone at any time.
That’s where two-factor authentication comes in. You’ve probably heard the term before – banks and security agencies constantly remind us to enable it. But what exactly is it, and how does it work?
In this definitive guide, we’ll walk you through the ins and outs of two-factor authentication, providing you with the knowledge you need to stay one step ahead of online threats. Don’t let cybercriminals get the upper hand – follow our guide now.
The definitive guide to using two-factor Authentication
The two-factor authentication is a common term that many banks and online security agencies mention. They tell us to ensure that this service or protocol is always turned on. Before addressing two-factor authentication, it is important to do all we can to improve online safety and security. These days, we do a lot online – from shopping, dating, and booking traveling tickets, to schooling.
The 2FA has proven to be a match for the current cyberattacks, online threats, and other crimes. Without proper two-factor authentication, all businesses – non-profits, startups, small businesses, and global companies can suffer substantial financial losses.
These activities mean that we reveal sensitive information about ourselves, including our online bank accounts. These days, there are too many eyes watching our online activities. The dark web has so many nefarious actors who watch a lot of people. It is now very common to have malicious attacks launched against businesses, individuals, companies, and governments.
These criminals work in syndicates with departments in every part of the globe. The evils of the dark web are expanding, and anybody (regardless of their technological advancement) can fall victim at any time.
What is two-factor authentication?
A two-factor authentication (2FA) is a type of security protocol whereby an account user will have to verify their ownership in two different ways when trying to access it. This is opposed to the one-level authentication, which usually relies on only a password. The two-factor authentication usually involves a password and another means for complete verification of the identity of the account owner.
The need for 2FA security: Increase in Cybercrime
Over the years, there has been an increased number of business websites and personal online accounts that have had their data/details stolen. The current level of Cybercrime being perpetrated these days has become more sophisticated. This means businesses and companies must neglect their old security protocols and look for more robust and reliable ones.
This can also take a toll on their reputation. A lack of a robust 2FA can lead to a devastating loss for a company. It may even threaten the existence of such businesses because they may lose their financiers and partners. Businesses that are hit can suffer the after-effects of compromised passwords for a long time. When important passwords are compromised, hackers can steal crucial financial information that may mean millions of dollars are lost.
The basics of two-factor authentication
Two-factor authentication, or 2FA, is a security protocol that helps ensure that whatever application or service you use double-checks each time you try to log in. It is a protocol that uses various systems to ensure that you are the authentic user of the password and, therefore, the actual owner is trying to log in. 2FA is a standard verification login policy that many payment websites, emails, and apps use.
There is also the theft of identities, private data, and many valuable digital assets. Hackers can use the funds for various purposes online when financial credentials are stolen. Apart from funding luxurious lifestyles, these funds can fund terrorism, drug activities, illegal hacking, and other dangerous lifestyles. As a business, when you lose your data to hackers (if you lose money), this can damage your credit rating. Due to poor password protection, entire cryptocurrency and bank accounts can be emptied overnight.
Two-factor authentication: A Brief Statistics on Victims
A survey was conducted recently, and it revealed that 15.4 million people in the US alone lost more than $16 billion to online thieves in 2016 alone. More incredible is that identity thieves could steal more than $107 billion within the last six years. With the recent increase in online theft and financial losses to syndicates, it is clear that two-factor authentication has come to stay.
Online apps and sites need to get tighter security. In addition, consumers must protect their online accounts and financial portals with solid passwords. The two-factor authentication is a great way to secure access to critical online accounts. It provides an additional security layer for such accounts, apps, or services not to be compromised easily.
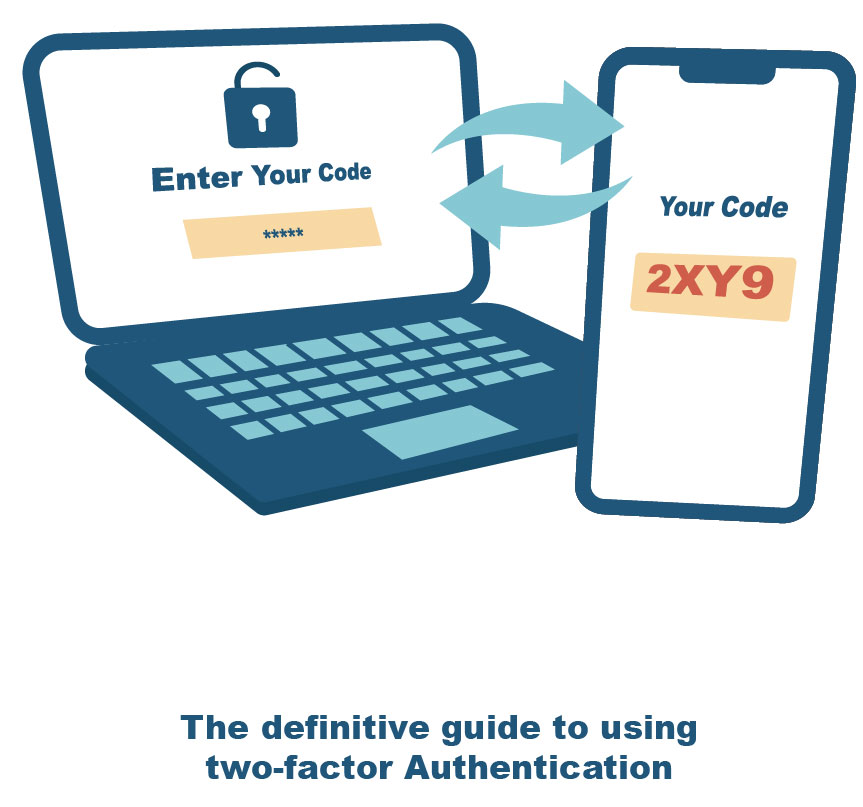
This is a two-factor authentication if you have received a numeric code or phone call from a website or service to help you gain access. You will need to get a code from the message to use as a way to gain access to the website, application, or service.
2FA is essential as a web security protocol because it helps neutralize compromised password risks. This means that if someone phishes, guesses, or hacks your password, they will not be given access to your private data. They will need further approval for the second factor. This means using a password as a single access permission factor is useless.
How does a two-factor authentication work
The two-factor authentication acts as additional security to ensure your password is always secured. This means that if you are trying to log into any online bank account or confidential application, the 2FA verifies your authenticity. Each time you input your password in the dialogue box and hit “enter,” it takes you to the next page that prompts you to enter a code sent to your phone.
This code is sent directly to your phone number. Some services or applications give you the option of answering a call. You get a code by answering the call. You input the same in the provided box as soon as you get the code. This way, the service or website can validate your identity. The 2FA is also helpful because it alerts you of any breaches to your account when unaware.
If you see a code sent to your mobile phone when you have not initiated any entry, you can stop the person from accessing your account. This is the importance of the two-factor authentication security protocol. The second factor of security is usually generated from one of the following:
1. An inherence factor: This is a more advanced form of the 2FA security protocol and usually has to do with biometric patterns of the body. This could be a voice print, an iris (eye) scan, or a fingerprint.
2. A code: Some 2FA protocols usually expect the original account owner to supply a specific code. This may be a code from a hardware/software token, a code from your phone, or the digits in your credit card.
3. A known answer to a question: Some 2FA protocols expect you to provide a pre-registered answer to a pre-determined question. Other variations include using a particular keystroke pattern or supplying a PIN (personal identification number).
4. The Location factor: This security feature grants access based on the user’s location. It relies on their geolocations or their IP addresses. Since users from specific locations may be prohibited, this protocol helps to ensure that.
5. Time factor: This security feature grants users access to the application or system based on time. For instance, if employees can work from 9 a.m. to 5 p.m. and the system has been configured to grant them access within business hours, any request to log in before 9 a.m. or after 5 p.m. is denied.
If you activate the 2FA function, no private account can be compromised. This means you can protect your financial information and personal details if you lose or have your phone stolen. It is almost impossible that someone will have second-factor information. You will be confident of your identity if you correctly use your 2FA apps and websites. This way, you will be given unhindered access to your account.
2FA levels:
When it comes to the application levels of the two-factor authentication feature, this is currently done in three different levels. The 2FA can currently be applied in three different levels such as:
1. The functional level: At the functional level, the 2FA is usually applied before the user can perform a particular action within the app. For instance, it could be sending a one-time password (OTP) to the user’s phone when they try to change a password after logging in.
2. The application level: The 2FA can be applied by applications to ensure security. For instance, it could mean that your payment app requires your password and fingerprints to access the application. Some other apps may prefer a password and a code sent to your mobile phone.
3. The device/system level: This type of 2FA is usually implemented if the user has to verify their identities before logging into a device or a system. For instance, this could mean users must provide passwords and a particular code to access the device/system. The code is usually generated instantly by a hardware token and sent to their mobile phones.









[…] ensure you stay safe from all online shopping scams, you must first determine whether or not the website is authentic. You can follow […]